Contacts
MILAN
Piazza della Repubblica 7-9, 20121 Milan
Ph: +39 02 45413500
Fax +39 02 45413509
E-mail gruppolercari@gruppolercari.com
GENOA
Via XII Ottobre 3, 16121 Genoa
Ph: +39 010 5446401
Fax +39 010 587898
E-mail gruppolercari@gruppolercari.com
Informational Risks and Data Submission
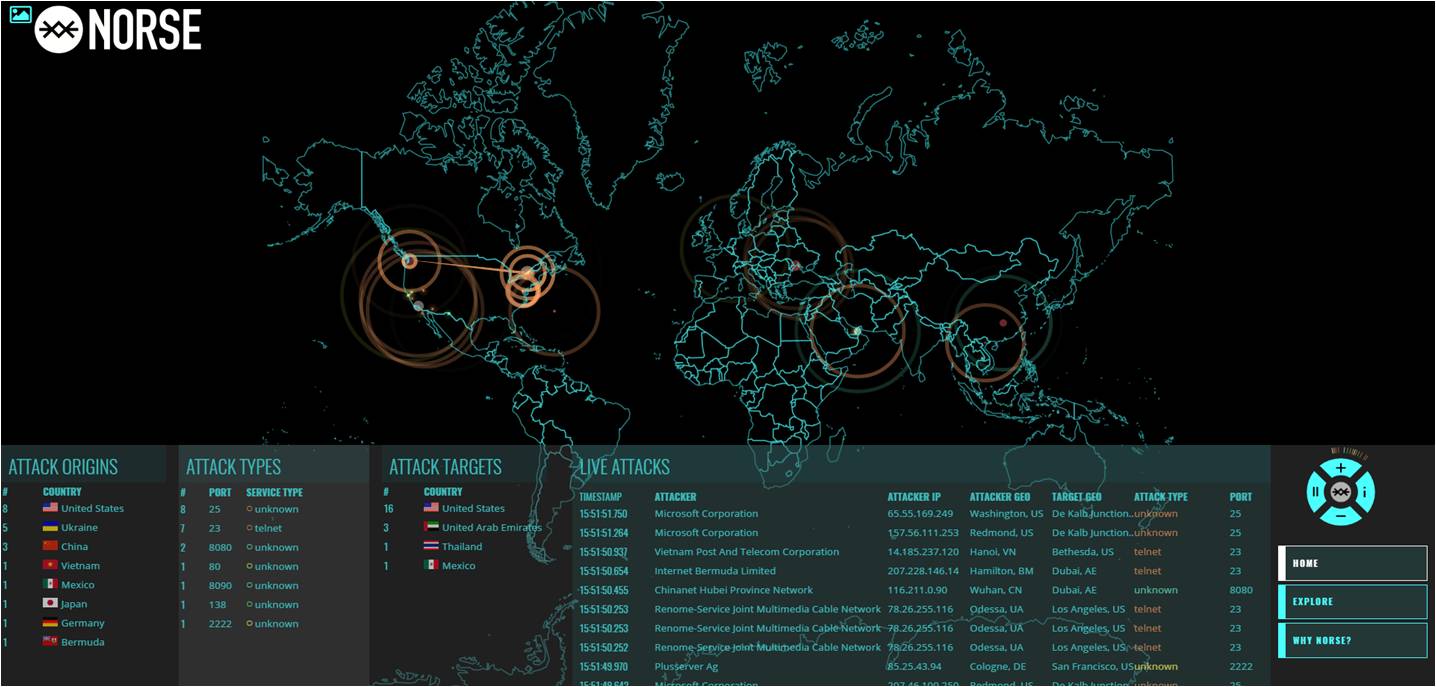
Rapid technological development and the proliferation of new IT systems and mass communication/interaction has certainly contributed to value creation, but it has brought with it an exponential increase in unforeseeable risks. Monitoring has therefore become a key factor, not only of a digital nature but also to equip ourselves with the tools and action plans necessary to confront this emerging risk which is often spoken about but which is still largely unexplored.
In fact, the majority of public and private sector organisations in Italy still underestimate or do not protect themselves against cyber risks, including those concerning the loss or theft of data (“data breaches”) - which have witnessed an exponential growth in Italy. The overall area of attack exposed by our digital civilization is growing faster than our ability to protect it. Those defending it are not effective enough: in the face of increasing investments in cyber security, the number and severity of attacks continue to increase. This is in a context, however, in which an estimated 2/3 of incidents are not even reported by victims.
A fully integrated world lies ahead of us in which cyber security will depend on the specific context. This involves the creation of a new approach to security management, no longer based on compliance but rather on a thorough risk analysis that allows specific security measures to be put in place.
An innovative service tailor-made for every needed
Lercari group, in diversifying the range of services offered , well beyond the field of appraisals , has developed an innovative package of services which allow an insured party to also avail itself , pending multi-risk policies , of an additional guarantee for cybernetic prevention and support at a limited cost.
Our solution
The package, aimed at insurance companies who wish to access it, is divided between preventive and/or assistance Warranties in case of cyber attacks (with a Call Centre open 24/7), data recovery, cost for reactivating affected IT systems and preventive services to analyse and improve vulnerabilities, IT assistance, secure system configuration (Wifi, Router, passwords, etc...). An Anti-Ransomware Application was also created, which was designed to prevent ransomware infection through operating system rules and by monitoring suspicious activities. The Anti-Ransomware prevents programs to execute on the system which have names and extensions typically used by ransomware. This prevents the ransomware from ever running and encrypting data or computer systems that are being monitored. The package is supplemented by a “Virtual Safe” with cloud technology and military grade encryption: in addition an online secure space of 512 GB can be accessed and used easily and intuitively from any PC or Mac.
"Digital Home"
At the discretion of the client, the insured party’s IT risk management package defined by Lercari as its “Digital Home” (a virtual place where the needs of its inhabitants for security and control, communications, leisure and comfort, environmental integration and accessibility are met through the convergence of services, infrastructure and equipment), can be complemented by a specific application to manage reputational risk through online media (InFusion, Intelligence Framework for Social Networks).
The on-line reputation
In fact, following the spread of social networks and their generalized use, nurturing an online reputation has become a priority - even for professional reasons. The application is based on open-source keyword searches (OSINT). All these searches are stored to later process and identify the results, enabling it to be analysed with data analysis techniques, classifying texts by subject, by feelings or by clustering. Thanks to its dashboard, “InFusion” allows searches to be easily managed and viewed, links to be checked manually, and screenshots and statistical graphics to be viewed.
The software is able to show the results and filter them. Using this tool, it is possible to analyse the process of gathering public information available on the net. Once the analysis has been completed an evaluation report of the client’s online reputation will be made available. Finally, there will also be a service to delete unwanted content.